Federal agencies are moving from Cloud First to Cloud Smart policies. In doing so, they have adopted one of the top Cloud Service Providers (CSPs). Most agencies already use more than one of the major cloud providers – like AWS and Microsoft – with others set to join the landscape. With this in mind, Palo Alto Networks launched their FedRAMP-authorized Prisma Cloud Solution, offering a comprehensive security platform covering cloud-native and multi-cloud environments.
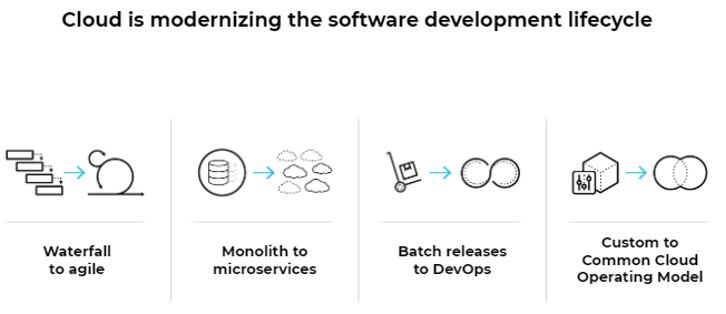
Multi-cloud environments are clearly here to stay. Yet, there is no standardization across them. Each CSP has its own set of application programming interfaces (APIs) and mechanisms for the control and management of its services, including development. Successful DevOps across CSP platforms requires development team agility and also a new approach to security.
One of the biggest challenges is a lack of visibility into the cloud providers themselves. It’s common for different functional teams to spin up public cloud resources into which security and operations teams lack visibility. That’s quite different from traditional data center environments where assets are inventoried when procured and can be readily tracked. Protecting virtual cloud services provisioned by distributed teams is difficult at best. When security does have visibility, they still need to manage multiple CSP consoles without having an authoritative source for all of the data.
Another big issue is the cyber talent shortage. CSPs are innovating so quickly that it’s simply hard to keep up. Each CSP environment brings hundreds of unique configuration controls, which also frequently change. Configuring across two or three of them compounds the problem. There just aren’t many people with strong knowledge of these environments; those who have this expertise are expensive and in high demand.
There is also the challenge of compliance across multiple cloud services. Resources deployed in the cloud still need to provide Continuous Diagnostics and Mitigation to adhere to compliance requirements like FISMA, CIS, ISO, and PCI. With so many cloud services provisioned by various teams, security professionals may not know what’s in their agency’s data “buckets.” Sensitive data making its way into misconfigured public cloud environments escalates both compliance and data breach risks. It also impacts the goal most agencies have of moving from a point-in-time Authority to Operate (ATO) to continuous ATO that addresses security requirements from the beginning of the development process.
These challenges make clear that automation is no longer optional for keeping agencies safe. Having a single platform where multi-cloud data can be integrated provides digital guardrails for all cloud services an agency uses.
That’s where Prisma Cloud comes in. Prisma Cloud is the only comprehensive cloud security platform covering both cloud and cloud native security. The platform provides predefined policies, advanced automation and machine learning templates that enable even security generalists to manage security across cloud environments. That’s far more efficient and cost-effective than needing expensive, hard-to-find subject matter experts.
Shifting-Left and Implementing IaC/CaC
Federal agencies develop and run some of the most complex and mission-critical applications. To do so requires deploying a large breadth of code into cloud environments: applications, storage configurations, user management, or even the entire infrastructure.
Developers often turn to infrastructure as code (IaC) tools to automate the creation of cloud environments. While it is efficient to quickly bring infrastructure up in a new cloud environment or region when needed, it’s also easy to make mistakes. Our research indicates that many developers don’t fully understand the IaC templates they download from the commonly used GitHub platform. That can lead to misconfigured cloud infrastructure by spreading configurations that were weak to begin with. Palo Alto Networks believes this is such a big problem that we recently acquired Bridgecrew, a company that offers the Checkov open-source tool for developers to scan templates so errors can be readily corrected.
CSPs operate under a shared responsibility model, where they secure the services they run, but customers own security for applications and configuration settings. New CSP customers often fail to understand their role in this model. In fact, Palo Alto Networks Unit 42 Cloud Threat Risk Report noted that at least 90% of all cloud breaches result from misconfigurations. Given the complexities, Gartner predicts¹ that “through 2025, 99% of cloud security failures will be the customer’s fault.”
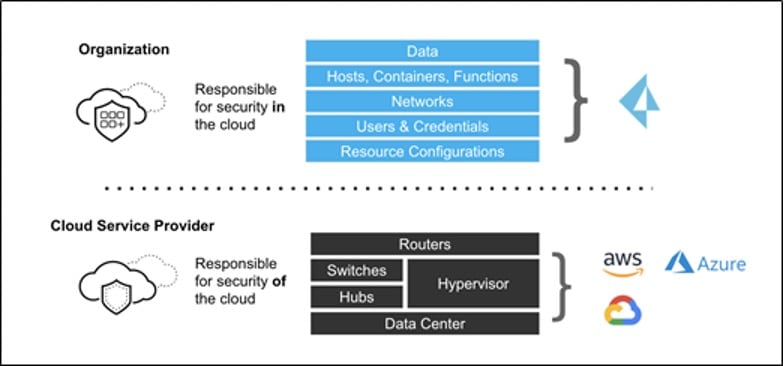
Cloud can rapidly scan the code and apply it against established security benchmarks and compliance frameworks, ensuring security standard adherence before code is ever executed. As a result, security no longer slows delivery of new capabilities to the warfighter. What’s more, the number of risks that could get into production and be exploited by enemies is considerably reduced.
Streamlining Cloud Identity and Entitlement Management (CIEM)
Identity management has been a challenge since the beginning of the computer age. Using multiple CSPs compounds that challenge. CSPs can have literally hundreds of configuration options for a specific user or role, creating many opportunities for things to be deployed incorrectly.
For instance, a given user may not have access to a particular cloud resource, but might later be assigned a role requiring it. Understanding permissions in CSP environments to make the permission change is very challenging. The complexity also makes it difficult to adhere to a least-privileged model. Instead, Prisma Cloud automates user permission identification, helping agencies adhere to least privilege and know exactly which users can access which resources.
Practically speaking, it’s nearly impossible to use native tooling or disparate point products to sync policies and overcome the operational burden of securing different clouds and cloud services. Prisma Cloud provides a single platform that streamlines multi-cloud security, providing the breadth of capabilities that complex CSP management demands.
For more information about Prisma Cloud from Palo Alto Networks, click here.