This is part two of a series detailing Army efforts to advance and integrate tactical cyber, electronic warfare and information operations within traditional forces. Part one can be viewed here.
In the not-so-distant future, commanders and infantry units will need to have a better understanding of cyber effects and capabilities.
The Army’s third annual Cyber Blitz experiment, hosted at Joint Base McGuire-Dix-Lakhurst in New Jersey, sought to test new capabilities, concepts and forces for the Army in bringing tactical cyber, electronic warfare and information operations to the battlefield. As the Army continues to experiment with introducing cyber forces and capabilities from the higher levels of government down to the tactical edge, commanders with traditional units must gain a notional understanding of what cyber can bring to them and how it can shape their scheme of maneuver.
“It was hugely educational for us as a [brigade combat team] … Generally we’re aware of a lot of capabilities that are out there, but this is typically above the BCT’s level,” Lt. Col. John Newman, deputy commander of 3rd Brigade Combat Team, 10th Mountain Division (the unit that Cyber Blitz planners were integrating new cyber units with), told Fifth Domain.
He added that the capabilities that could be available to a brigade in the tactical fight in the 2025 time frame were eye-opening.
Newman said one of his big takeaways from the experiment was the benefit of the additional cyber personnel that increased the size of his overall force. Wittstruck described one of the key premises of Cyber Blitz was providing force augmentations — additional personnel not typically within the unit — to the brigade in the form of cyber capability.
“As you give us all this increased capability that’s great, but if I don’t have the people there to help plan it, to help execute it, to help inform the leaders of what their operations are, then all the capability in the world is not helpful,” Newman said.
Currently, the only organic cyber/EW-related component to a brigade are cyber and electromagnetic activities (CEMA) planners and EW capability. The expeditionary CEMA teams and support detachments are add-ons to the unit.
How to provide situational awareness
While the commander doesn’t need to be fluent in geek-speak, he has to at least have a good understanding of his virtual battle space, which will now fall under his purview.
Officials described the need for every soldier to be CEMA literate in order to understand the context for how CEMA will fit into their mission or how it can support CEMA, be it intelligence or infantry actions.
“It’s easy to say that we need more situational awareness of what’s going on in the cyber realm but at the same time I don’t need the wire diagrams of where all the computers are,” Newman said.
“We’ve been able to look at some of those different programs and provide at least our opinions of where that line is between this is really good information for the cyber operators and then this is the cutline as to what I would need to know as the [defensive cyber operator]. That was the feedback we were able to offer from my perspective.”
RELATED
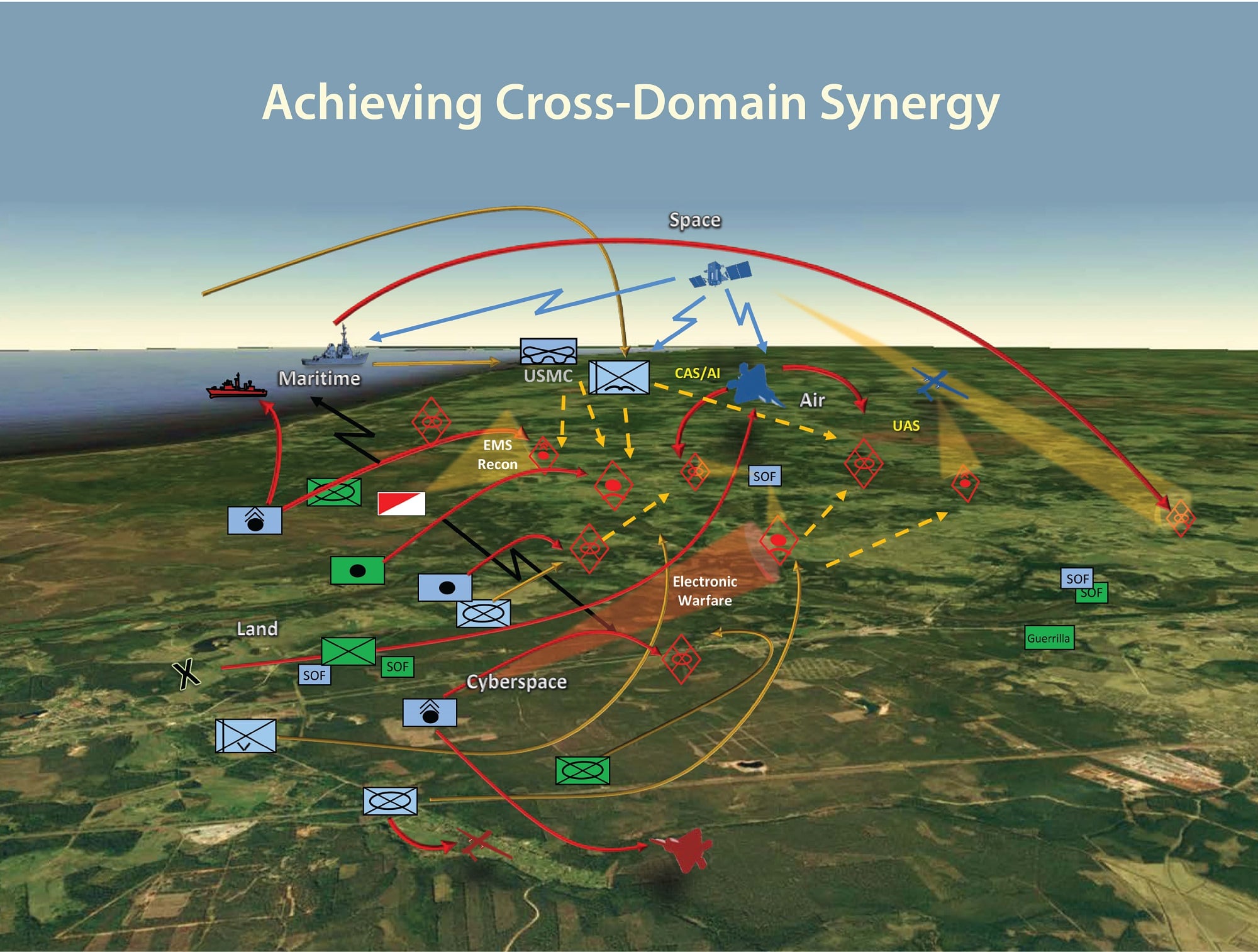
For basics, the brigade staff will need to understand where an adversary would logically be within the cyber domain, what aspects and entities within that are critical to him to be able to operate within in the cyber domain, effectively identify those and pass them to someone who can remediate them, Chief Warrant Officer 2 Robert Newbanks, an intelligence official within the brigade, said during a walk-through of the command post.
Maj. Camero Jong, an intelligence officer within the brigade, said he is worried about friendly space, enemy space and the neutral space in between, even coordinating with the network folks and notifying them of points he would target on friendly networks if he were the enemy.
Newman noted that all the situational awareness tools allow him to track the progress and operations of cyber personal in cyberspace. He wants to know if the cyber folks are getting caught up somewhere on their mission just as he’d want to know if an infantry company meets heavy resistance somewhere and will take longer than expected to reach the object. In communicating with the cyber team, Newman can start to craft a Plan B if needed.
How to compete with Russia
One of the big takeaways for Newbanks was how far down the enemy’s command chain they used cyber and EW to effect maneuver forces.
Newbanks said there is still some work to be done in understanding the granularity of how the enemy coordinates kinetic fires and activity in the electromagnetic spectrum.
“It got everybody’s attention when that [Ukrainian] field artillery unit was decimated in 20 minutes,” Wittstruck said of Russia’s operations in Ukraine. It started with drone datalink interruptions preventing aerial eyes, then the loss of communications, with the next sound being inbound field artillery.
“That sent a clear message that some of our regional peers are looking very seriously at how do they get to the pointy edge of the spear with those kind of advanced capabilities to shape the battle space for what’s to come next,” Wittstruck said.
Newbanks also said that the team took lessons on the tactical EW front, noting that after the counter-improvised explosive device fight in the war on terror, the force writ large doesn’t have a good sense of what electronic attack and electronic support capabilities can offer, especially against a near-peer adversary.
Part three examines the emerging units the Army is using Cyber Blitz to inform.
Mark Pomerleau is a reporter for C4ISRNET, covering information warfare and cyberspace.







