With greater fervor than in recent years, U.S. military leaders say they are engaged in a heightened global conflict every day in the information space.
“I don’t think the salvo has been fired, they’re firing. We’re at war right now in cyber. We’ve been at war for a decade. If Gen. [Paul] Nakasone or Gen. Glavy, they’d tell you, we’re pouring oil over the castle walls every day,” Gen. Robert Neller, the commandant of the Marine Corps, said during a panel discussion Feb. 15.
Adversaries in the information domain — be it cyber, social media, influence, electromagnetic spectrum — are trying to leverage these capabilities to gain an advantage without firing a shot. In recent months, officials said that within this information sphere, the United States is engaged in what is referred to as phase 3 operations with its enemies. This comes despite the fact that formally, there is no declared conflict and physical forces are not involved.
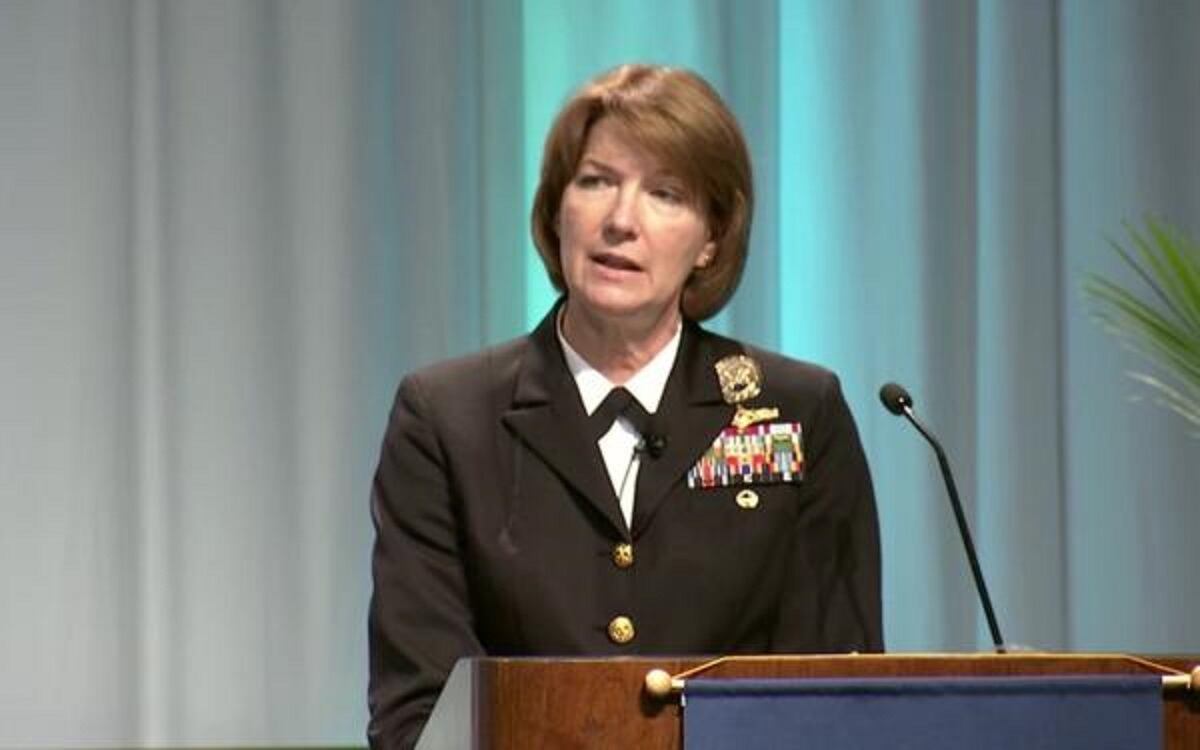
“I’ll reaffirm that we are in phase 3 in the cyber domain today. There’s no question about that in my mind,” Vice Adm. Nancy Norton, director of the Defense Information Systems Agency and commander of Joint Force Headquarters-Department of Defense Information Networks, said Feb. 14 at the West 2019 conference.
Within the military’s six-phase cycle for each conflict, phase 3 refers to dominating adversaries in which forces focus on the exploitation, pursuit, and destruction of the enemy in order to break the will to resist. JFHQ-DoDIN is a subordinate headquarters to U.S. Cyber Command that is responsible for defending DoD’s networks.
“We very definitely are in contact with adversaries — not always knowing who that adversary is in the cyber domain — but certainly that there are those trying to attack our networks, whether that’s our defense networks, contractor networks or the commercial aspects of the network that we ride on,” Norton said.
Gen. Paul Nakasone, commander of Cyber Command, wrote in testimony to the Senate Armed Services Committee Feb. 14 that adversaries are taking risks to gain advantages without escalating to armed conflict. They’re doing this as a way to gain an advantage through theft of intellectual property, influence, election interference and actions against critical infrastructure, all of which are conducted through the information domain.
Nakasone added that JFHQ-DoDIN uses network sensors as a way to determine cyber risks and to help build the requirements finding vulnerabilities in DoD networks.
“The data JFHQ-DoDIN collected in this effort proved that state-sponsored adversaries in cyberspace are conducting rapidly evolving campaigns to hamper the routine functions of the DoDIN and to find seams in its defenses. DoDIN protections are robust, but we must continue to innovate in our data collection and analysis to build resilience and counter the dynamic nature of adversary threats,” he said.
To help combat this, Cyber Command has taken the approach that it must “persistently engage” an adversary that is in constant contact with U.S. targets every day in order to defeat and deter such threats. As part a doctrinal shift for the Army, service leaders are beginning to recognize the necessity to engage adversaries in what’s called the “compete phase,” short of armed conflict.
“In a state of continuous competition, China and Russia exploit the conditions of the operational environment to achieve their objectives without resorting to armed conflict by fracturing the U.S.’s alliances, partnerships, and resolve,” a new concept document, titled “U.S. Army in Multi-Domain Operations 2028," reads.
RELATED
Enemies “see continual conflict on a spectrum or on a continuum,” Lt. Gen. Eric Wesley, deputy commanding general of Futures Command, told reporters in December. He added that Wesley said given the effectiveness of information as a weapon today, the time available to move from peace to war or “right of conflict” is a narrow window.
“If you miss that window, you find yourself well behind,” he said.
As such, this approach of constant contact extends even beyond cyberspace to the traditional military realm with all other functions of information.
“While we’re heavily involved in being prepared to support that high end conflict, most of our time is spent left of that kinetic conflict and I would describe in information warfare while the rest of the warfare areas are involved in the high end conflict, we consider the high end conflict now,” Vice Adm. Matthew Kohler, deputy chief of naval operations for information warfare and director of naval intelligence, told C4ISRNET in an interview at West 2019.
“Constant contact with the enemy in terms of cybersecurity, being able to operate within the [electromagnetic spectrum], all of those we consider ourselves in contact with the adversary now. It’s a … different kind of approach in terms of how we operate.”
In any warfare area whether it’s air, surface, subsurface, to include the information domain with things such as cyber or electronic warfare, Kohler said intelligence support is the same. It’s about trying to figure out who the adversary is, what are their capabilities, what are their intentions. Then it’s being able to bring that perspective to an adversary that operates in cyberspace or the electromagnetic spectrum.
This extends to the tactical arena as well. The Marine Corps is beginning to stand up new units called MEF Information Groups (MIGs), which will be aligned to all three Marine Expeditionary Forces and integrate cyber, EW, signals intelligence, communications and information operations under one unit.
“With the MIG, what I really want to be able to get after, it truly is a multidomain fight. In other words, what are the information battlespace things we’ve got to deal with, what are the cyber things, what are the electronic warfare things, what are all of these, in particular, non-kinetic attributes and then how do I fold them into a combined arms fight,” Lt. Gen. Joseph Osterman, commander of I MEF, said Feb. 13 at West 2019.
“Because, again, it gets a little more complex … I might very well be in a phase 3 fully engaged, fully blown cyber fight against my enemy but in a phase 0 physical fight.”
Mike Gruss of C4ISRNET contributed to this report.
Mark Pomerleau is a reporter for C4ISRNET, covering information warfare and cyberspace.