Sophisticated adversaries have been leveraging the electromagnetic spectrum to create significant dilemmas for U.S. and allied forces, say officials, and transformative efforts are needed to deal with an increasing complicated threat.
“China is outspending us probably 10 to 1 on trying to figure out how to use and manipulate the electromagnetic spectrum. Russia showed us what they’re going to do with it in their incursion into Ukraine … Electromagnetic warfare, electronic warfare at the maneuver level,” Gen. Paul Selva, vice chairman of the Joint Chiefs of Staff, said at the annual Association of Old Crows symposium held Nov. 28 in Washington, D.C.
“We haven’t designed ourselves to fight that fight. They have demonstrated that they are not only willing, but they’re [also] capable of deploying and employing electronic countermeasures at the ground and maneuver level. It is a reality that we are going to have to adjust to.”
The capabilities forces need
For the Army, it’s not going to be one thing, Col. Mark Dotson, the capabilities manager for electronic warfare at the Cyber Center of Excellence, said at the symposium Nov. 27. There have to be layered capabilities and effects, each increasing range and sensing capability.
“We’re still sorting through that,” Dotson said, noting the need to develop from the current tactical focus all the way to the strategic level.
“We’re trying to expand our scope and get into what are those other things we need. Do we need artillery delivered capability? Do we need loitering munitions? Is it going to manned or is it an unmanned aircraft?”
In addition, Dotson said, the Army needs systems integrating EW, cyber and signals intelligence, and the service has started generating requirements working with the Intelligence Center of Excellence and the Cyber Center of Excellence.
“I think SIGINT and EW go hand in hand, so us not sharing going forward and working like a team like we do now makes no sense,” Col. Jennifer McAfee, Dotson’s counterpart for Terrestrial and Identity at the Army Intelligence Center of Excellence, told C4ISRNET in a November interview.
McAfee added that the team is also joining up with the other centers of excellence to ensure that when they are pursuing requirements for airborne or ground systems, the Intelligence and Cyber centers are plugged in to leverage EW expertise and not create duplicative efforts.
RELATED
Geolocating solutions
Others across the joint force have expressed the desire for more decoys, physical or non-physical, to confuse or confound enemy systems.
“It’s network electronic warfare from air, sea and land; it’s smart warfare combined with advanced decoys, whether they’re physical decoys or cyber decoys out there; drones, swarms and jamming drones,” Col. John Edwards, commander of the 28th Bomb Wing, said at the symposium.
“Things that go out there to where an air defense operator cannot distinguish between what is cyber and what is real out there.”
Such aerial systems can be used to either overwhelm or distract air defenses, allowing strike aircraft to penetrate, or take the point jamming the air defenses and thus assuming all the risk leaving the more expensive and manned systems in the rear.
On the ground side, officials have also discussed the need for more investments in decoys.
Lt. Gen. Stephen Fogarty, commander of Army Cyber Command, told reporters in August that big investments needed to be made in this area. He envisioned forces being able to drop a decoy emitting strong signals off a truck at a fork in the road, thus drawing enemy attention to it.
“Now we’re presenting multiple dilemmas to the adversary,” he said.
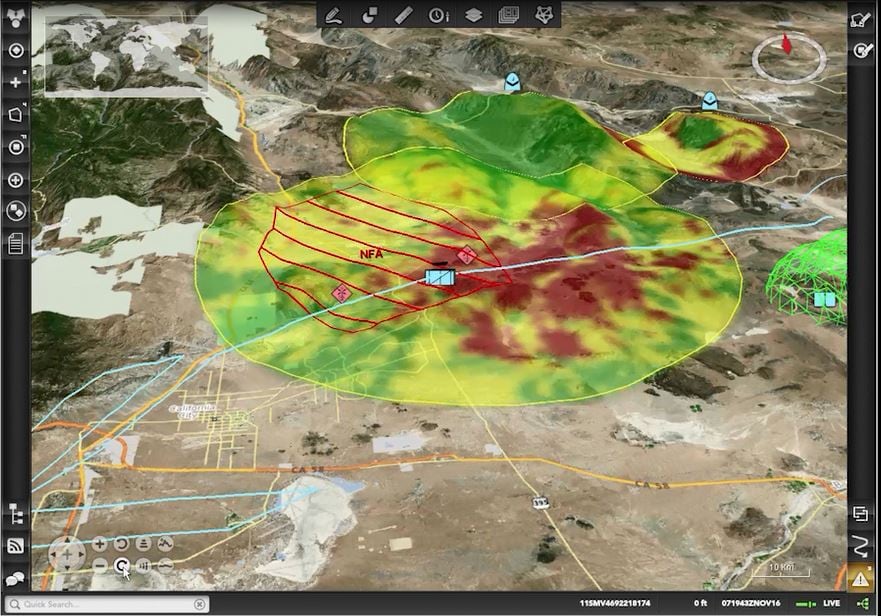
One of the difficulties of modern warfare is all jammers and sensors emit some kind of a signal in the electromagnetic spectrum, meaning they can be geolocated and targeted. This means if an enemy wants to use it, they have to take into account a risk calculus in revealing their position.
“Jammers are emitters, emitters are targets. I think that’s something we really ought to be thinking about,” Selva said. “If you’re going to operate in an electronically dense environment … the tools actually reveal their position."
Similarly, decoys can be used to throw adversaries off the trail of friendly forces or distract from other items forces might want to protect.
”If I have something like a counterfire radar, that’s really important to me. Maybe what I want to do, again, is push an alternate threat to the adversary," Fogarty said.
In these complex environments, Selva said forces need to be able to identify, localize and characterize the jammer. If that’s possible, then forces can decide what to do with it. If the answer is they want to kill it, they have to have a tool to kill it.
“If you can’t do all three of those things, the jamming is very effective,” he said.
Mark Pomerleau is a reporter for C4ISRNET, covering information warfare and cyberspace.








