The Pentagon has finalized the long anticipated cybersecurity standards contractors will have to follow before winning contracts from the Department of Defense, a new process called the Cybersecurity Maturity Model Certification (CMMC) 1.0.
The model is a tiered cybersecurity framework that grades companies on a scale of one to five based on the level of classification and security that necessary for the work they are performing.
“The government and the contractor community must keep working together to address real and growing cybersecurity threats, and we need a robust response to protect our infrastructure, information, and supply chains,” said David Berteau, president and chief executive of the Professional Services Council, a trade association for federal contractors. “With today’s announcement, DoD has achieved a significant milestone.
Here’s what industry officials need to know about the version finalized Jan. 31.
Why it was needed
Previously, the Pentagon did not have unified standard for cybersecurity that businesses needed to follow when bidding for contracts. Companies could claim to meet certain industry standards for cybersecurity, but those assertions were not tested by auditors, nor did the standards take into account the type of work a company was bidding to complete. Since then, defense officials have said that cybersecurity is not a one size fits all approach.
In the meantime, adversaries have discovered it is easier to target unsuspecting down tier suppliers, rather than prime contractors.
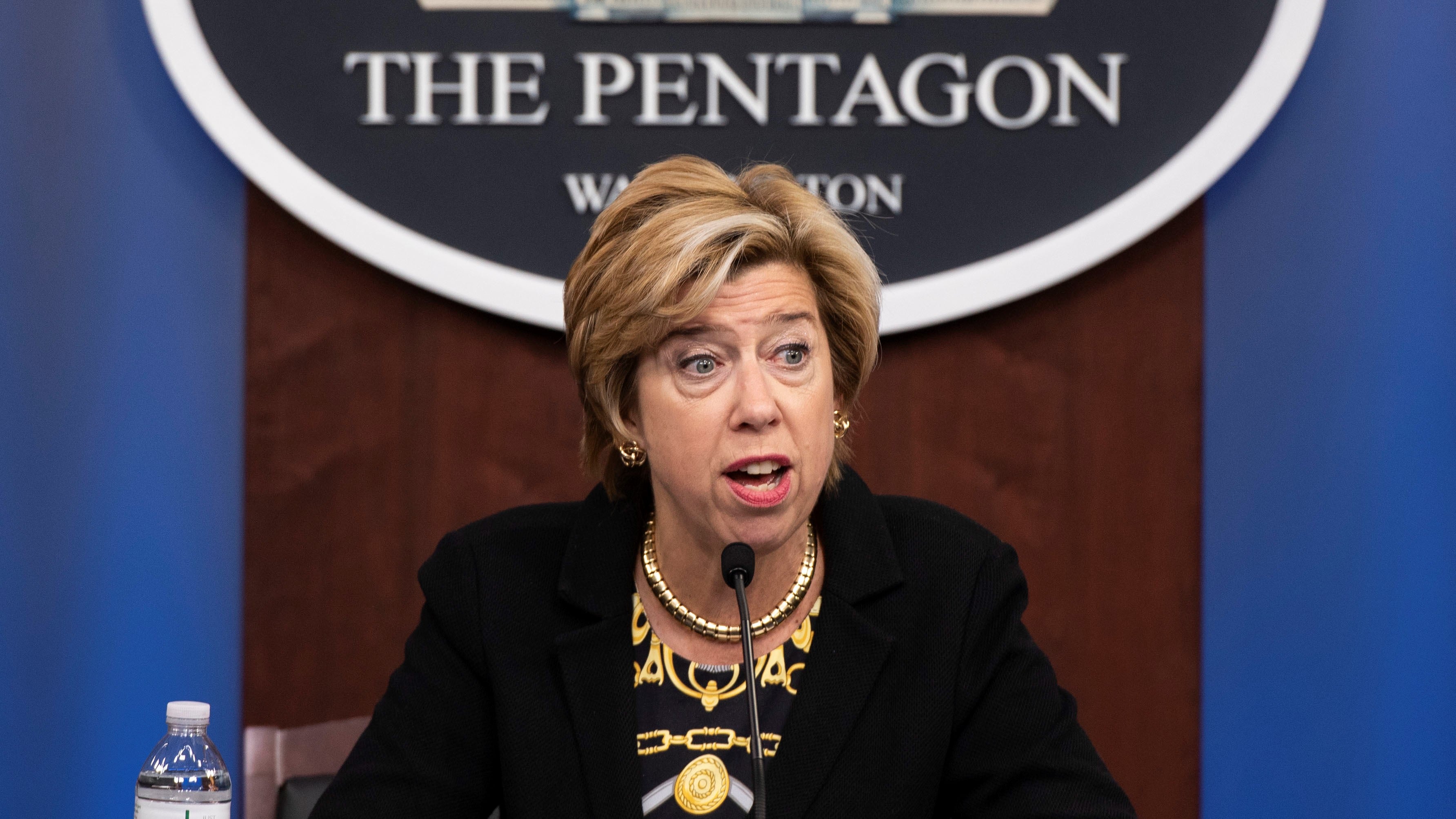
“Adversaries know that in today’s great power competition environment, information and technology are both key cornerstones and attacking a sub-tier supplier is far more appealing than a prime,” Ellen Lord, the under secretary of defense for acquisition and sustainment, told reporters in a briefing at the Pentagon Jan. 31.
Officials have said cyber theft by adversaries costs the United States about $600 billion a year.
What will change?
Contracts will mandate bidders reach a certain level of certification to win specific jobs. For example, if businesses aren’t bidding on a contract that has extremely sensitive information, they must only achieve the first level of certification, which involves basic cybersecurity such as changing passwords and running antivirus software. More sensitive programs will require more stringent controls.
Smaller companies down the supply chain will not, however, have to have the same level of certification as primes, said Katie Arrington, chief information security officer for the Office of the Under Secretary of Defense for Acquisition and the point person for the certification.
Another significant change with the new process is the creation of an accreditation board and assessors. The board is an outside entity, separate from DoD, that will be charged with approving assessors to certify companies in the process.
The accreditation body was formed earlier this month and officials are working on identifying and training the assessors, which will be called Certified Third-Party Assessment Organizations (C3PAO).
What’s next?
Officials explained Jan. 31 that CMMC will follow a crawl, walk, run approach to ensure companies aren’t unprepared for the change. The accreditation board is in the process of training the auditors that will oversee the certificaion. Once the requirements are met, a company’s certification is good for 3 years.
In the meantime, DoD plans to release 10 requests for information and 10 requests for proposals that will include the new cyber standards this year. The first solicitation could come as early as June.
She added that all new contracts starting in fiscal year 2026 will contain the cybersecurity requirements, however, Lord noted that they will not be not retroactive to previous contracts.
Mark Pomerleau is a reporter for C4ISRNET, covering information warfare and cyberspace.