Lockheed Martin has unveiled a model for measuring the cyber resiliency of weapon systems.
Dubbed the Cyber Resiliency Level (CRL) model, the defense giant boasts this is a first-of-its-kind concept focusing exclusively on defense weapon systems, mission systems and training systems — not IT systems.
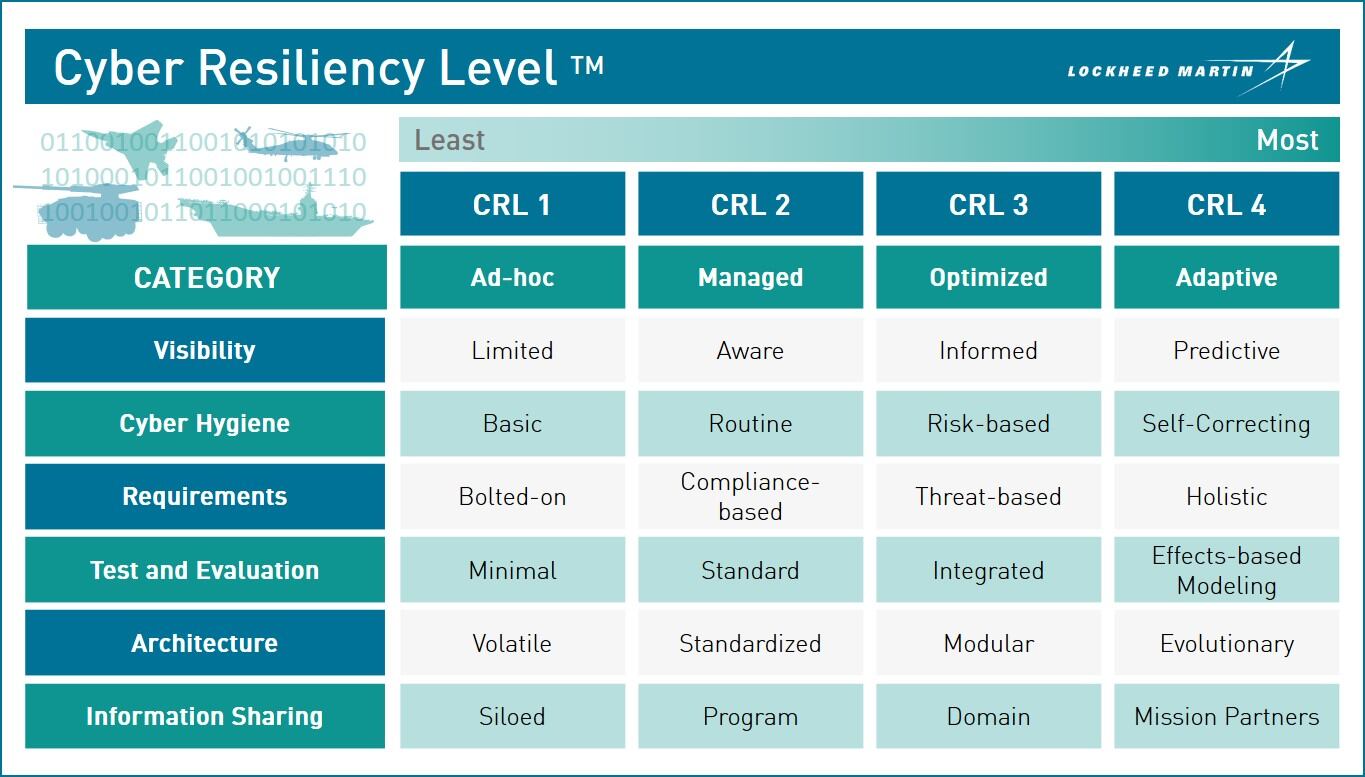
The model lists four resiliency levels — ad-hoc, managed, optimized and adaptive — that six categories are weighed against.
The categories include:
- Visibility: the ability to efficiently sense, collect and infuse data;
- Cyber hygiene: the ability to assess and maintain the effectiveness of cyber controls;
- Requirements: the needs for certain capabilities, which officials said is commensurate with mission importance and risk to operational environment;
- Test and evaluation: the ability to measure the effectiveness of controls against mission objectives;
- Architecture: the ability to maintain a capability against cyberattacks; and
- Information sharing: can a program share threat information with other programs.
The reason for developing this model was threefold, Jim Keffer, director of cyber at Lockheed Martin Government Affairs, told reporters Aug. 13 at Lockheed’s Arlington, Virginia, Global Vision Center.
First was urgency. Threats continue to target critical systems and the Department of Defense did not start writing requirements for cybersecurity of weapon systems until the 2014-2015 timeframe, Keffer said.
He added that forces are in constant contact every day.
Second, Congress has been demanding since 2016 that DoD conduct audits on the cybersecurity of its weapon systems, as well as define how to mitigate vulnerabilities found. Keffer said the Lockheed model achieves this.
Third, Keffer stressed that war fighters need this type of capability in order to protect themselves.
Lockheed officials explained the model is being used internally on 10 pilot programs; they declined, however, to offer specifics regarding the customers or systems within the pilots.
The model is designed to be flexible and adaptable over time as threats or technology changes, officials said. Moreover, it can be applied to the development of new systems, as well as sustainment efforts for legacy systems.
Mark Pomerleau is a reporter for C4ISRNET, covering information warfare and cyberspace.








