The Department of Defense wants to hear from industry leaders about the Pentagon’s proposal to grade contractors on their cybersecurity.
The Defense Department is focusing on the cybersecurity of its suppliers. According to experts, while DoD requires compliance with certain standards released in 2017 from the National Institute of Standards and Technology, many companies blew past those deadlines and requirements.
Now, DoD is rolling out what it calls the Cybersecurity Maturity Model Certification, a framework that grades companies on a scale of one to five. A one designates basic hygiene and a five represents advanced hygiene. The scale is flexible, officials said, and will adapt over time. Right now, Pentagon leaders want input from companies on what controls work and which don’t.
Feedback is due before Sept. 22.
“Since it’s a collaboration, with over 7 percent of my data on your networks, it’s no longer a me-or-a-you thing, it’s a we thing,” Katie Arrington, chief information security officer for the Office of the Under Secretary of Defense for Acquisition, said at the Billington Cybersecurity Conference in September. “I need to know what [controls] are not useful and how you would take that control and make it a requirement,” she said.
For example, the Pentagon wants to know the best ways to measure access control and multifactor authentication.
Understanding the threat
The defense industrial base has long been a target for foreign espionage. U.S. government officials have said that while much of the information breached in the past several years from private businesses was not classified by itself, in aggregate, the data revealed a great deal of sensitive information about military programs.
Moreover, many small companies far down the supply chains of large defense primes lack even basic cybersecurity and in some cases don’t even have IT personnel.
Foreign actors recognize this fault and have targeted those firms.
“Little [companies], the Chinese know are the ones that are just not going to have the resources,” Michael Flavin, director of technology sales at Saalex Information Technology, told Fifth Domain. “It’s like having a big 20-story bank and there’s a fire ladder. The first floor is everything’s locked down and armed guards but if you’re able to get up the ladder or come in a side window and just break a pane of glass, you’re in the whole thing. You come in thorough the side.”
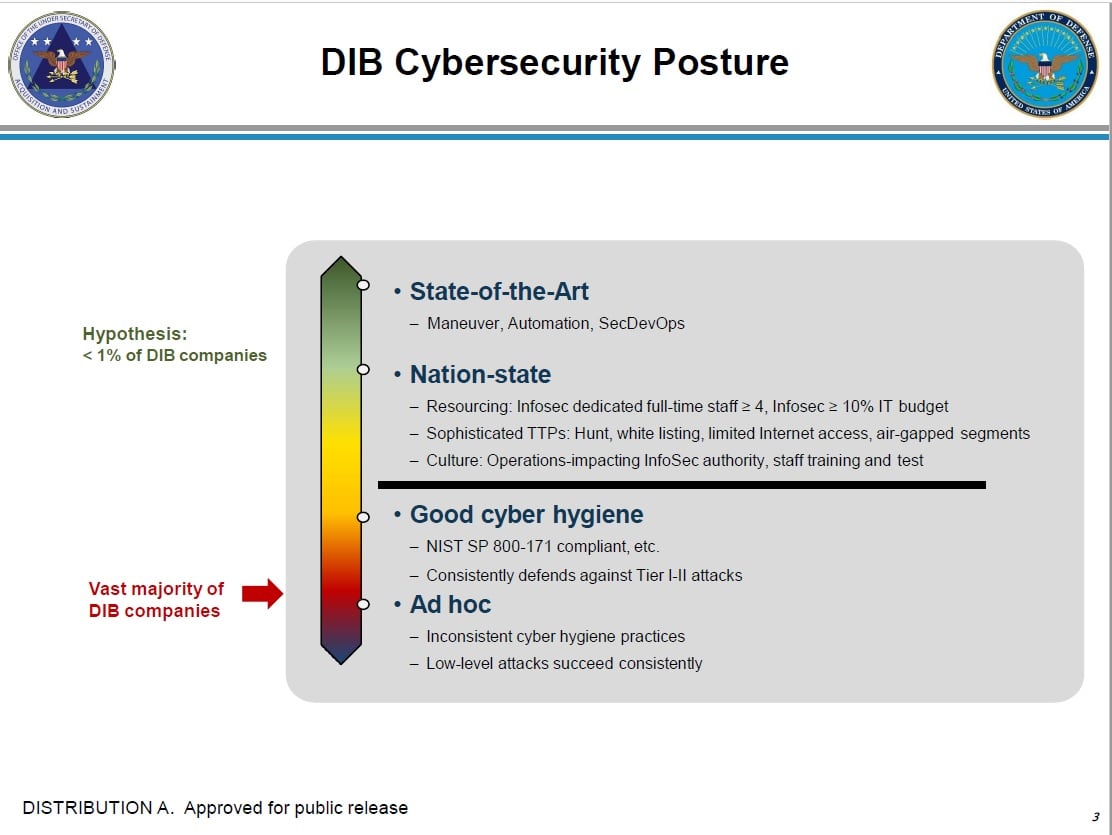
According to an August presentation from Stacy Bostjanick, director of the Cybersecurity Maturity Model Certification Policy, the vast majority of the defense industrial base has ad hoc cybersecurity. The Pentagon described those companies as ones with inconsistent cyber hygiene practices and those that are susceptible to low-level attacks.
Congress has noticed this growing threat and vulnerability.
“It’s no secret that U.S. supply chains are a target for China and other nations seeking to undermine U.S. competitiveness,” Sen. Mark Warner, D-Va., vice chairman of the Senate’s Intelligence Committee, wrote in an emailed statement. “In light of these threats, we need a comprehensive, government-wide technology strategy to reduce vulnerabilities and protect against any attempt to penetrate or exploit our networks. We also need to make sure that every link in the chain is adequately prepared to fend off unwanted interference.”
To combat this problem, Pentagon leaders have begun to equate security among the cost, schedule and performance metrics that determine which firms can win contracts.
With the new standards, companies will have to ensure down-stream suppliers within its chain are compliant with the requirements or they won’t be able to compete ― or recompete ― for contracts.
“By fall of 2020, CMMC requirements will be included in requests for proposals and will be a go/no go decision,” Ellen Lord, undersecretary of defense for acquisition and sustainment, told reporters during an August briefing.
Mark Pomerleau is a reporter for C4ISRNET, covering information warfare and cyberspace.








